1、介绍
官网:https://kubernetes.io/zh-cn/
Kubernetes 也称为 K8s,是用于自动部署、扩缩和管理容器化应用程序的开源系统。
2、安装
通过 docker desktop 安装 K8s
a、docker desktop 中设置允许 K8s 随 docker desktop 自启动。
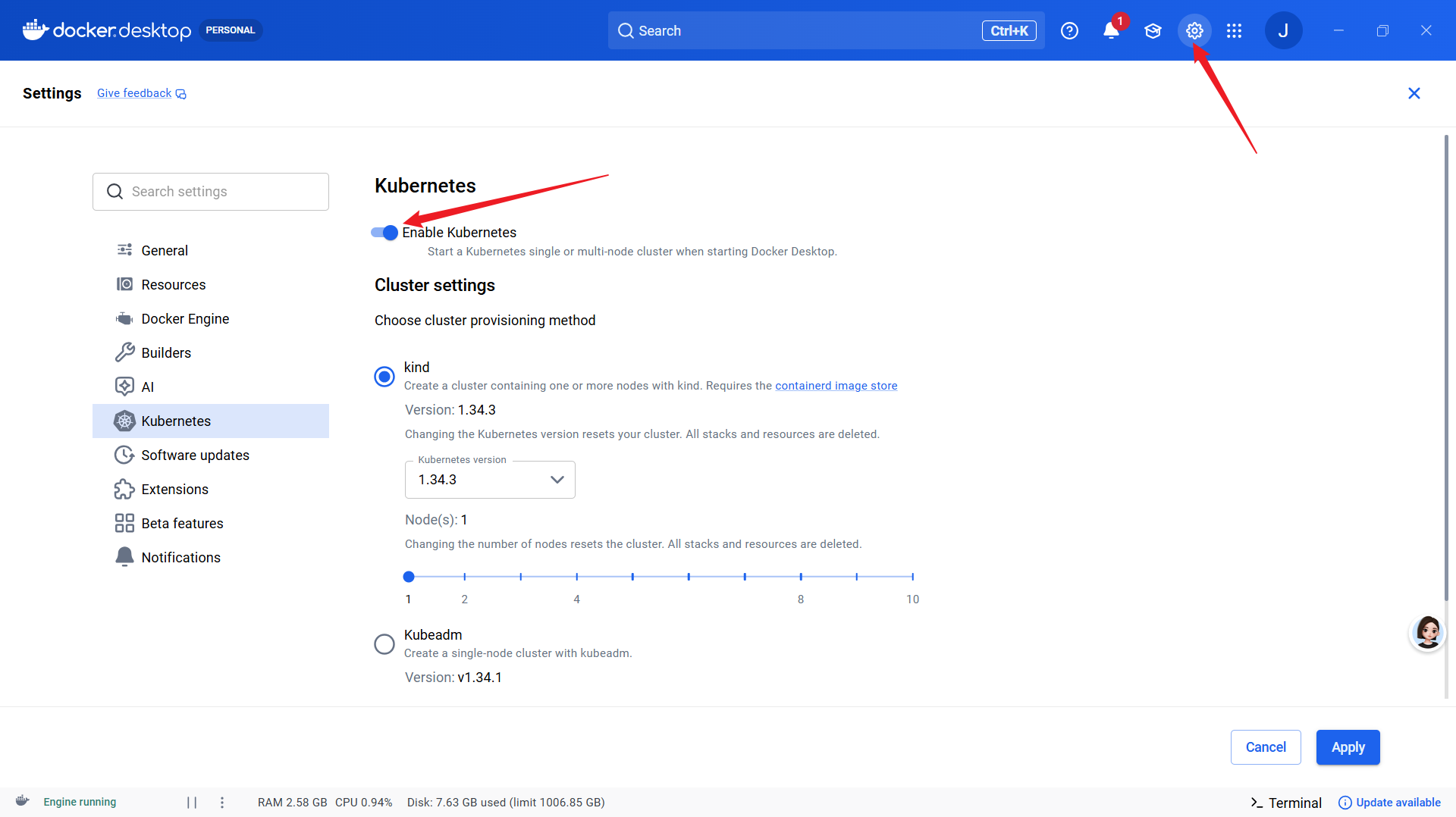
其中:
kind:多节点、自选K8s版本、支持节点故障、滚动更新、多节点调度
kubeadm:单节点
Show system containers (advanced):通过docker ps 可以看到K8s内部容器
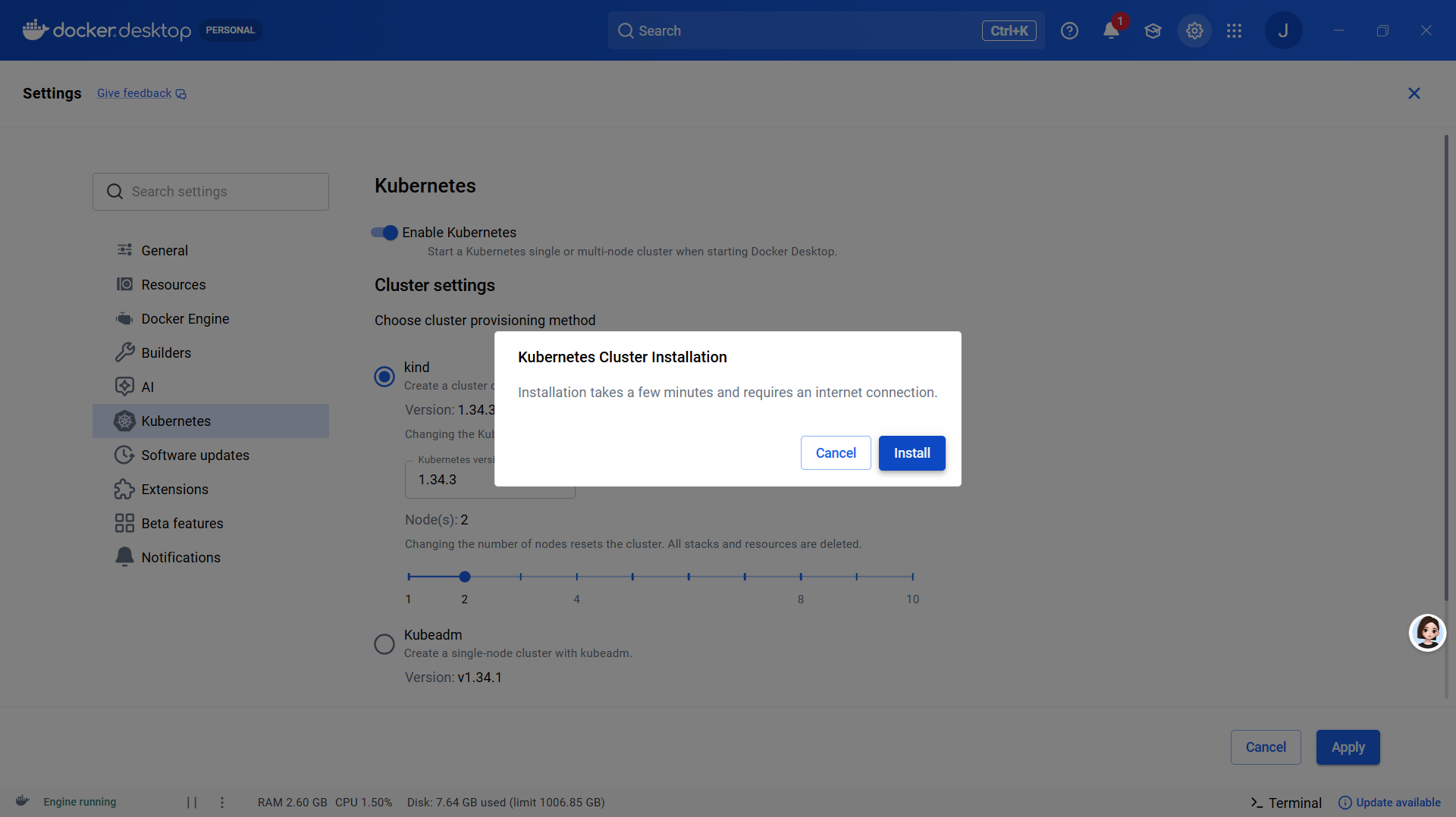
b、开始安装 K8s
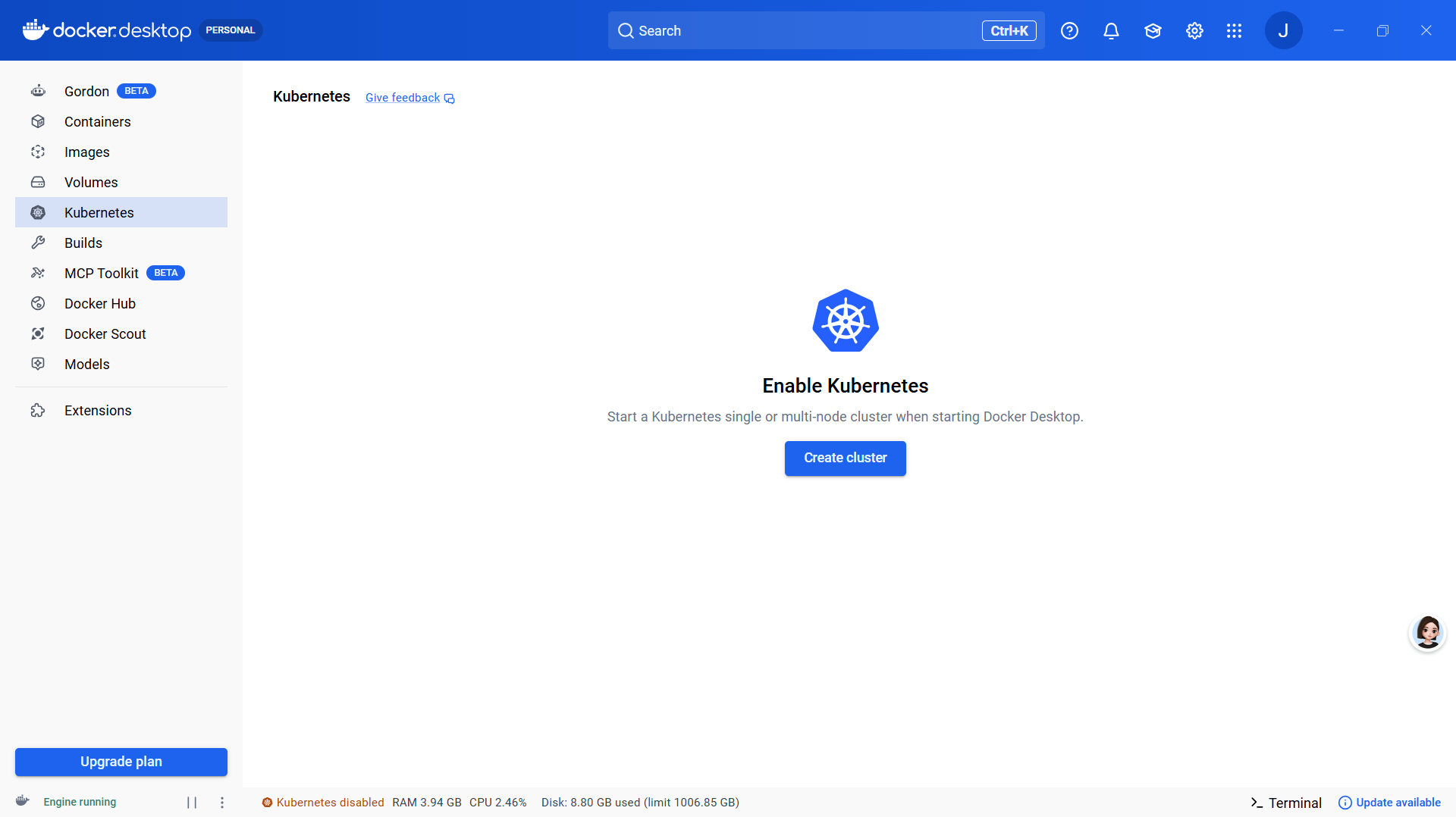
c、创建K8s集群
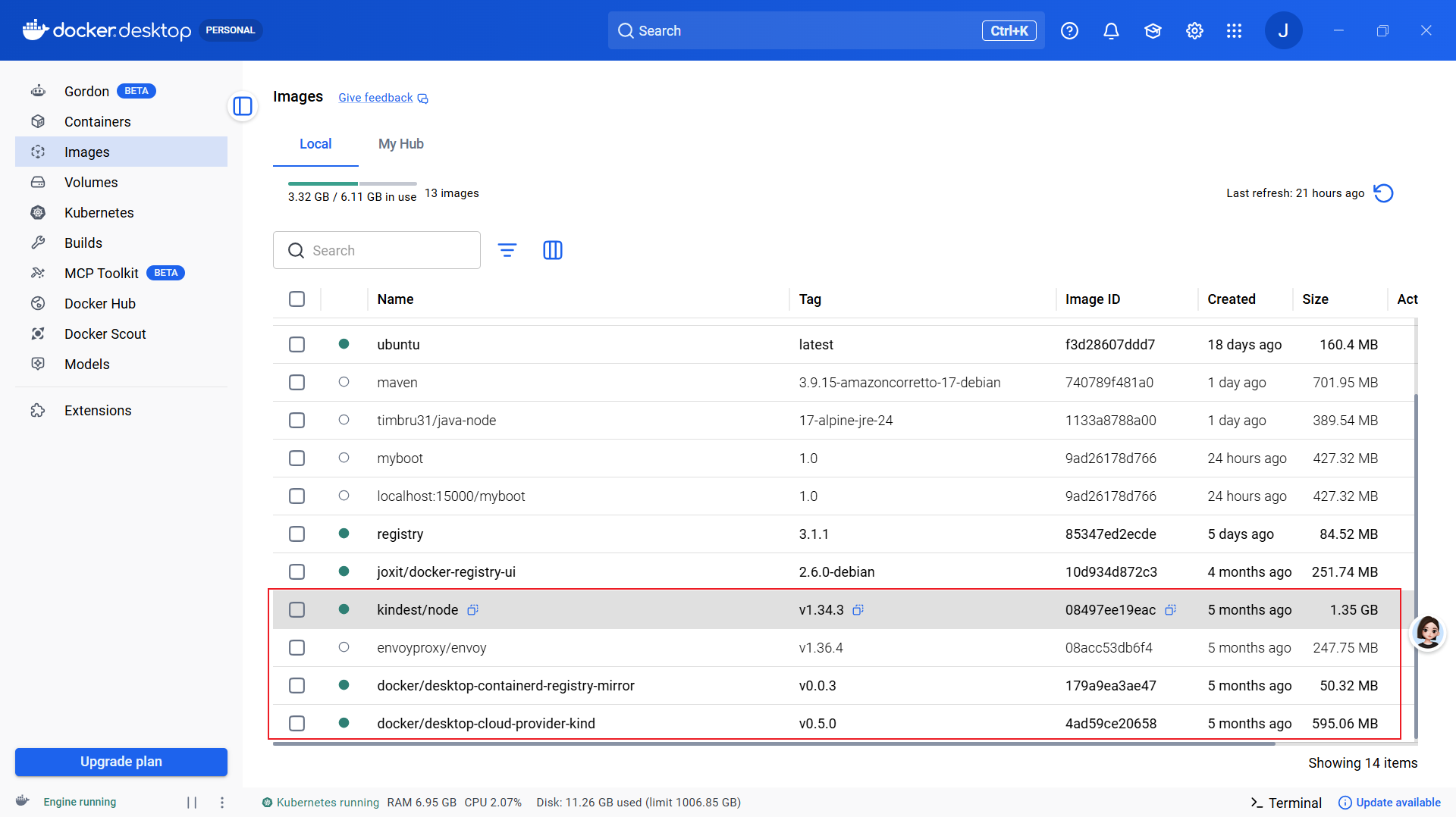
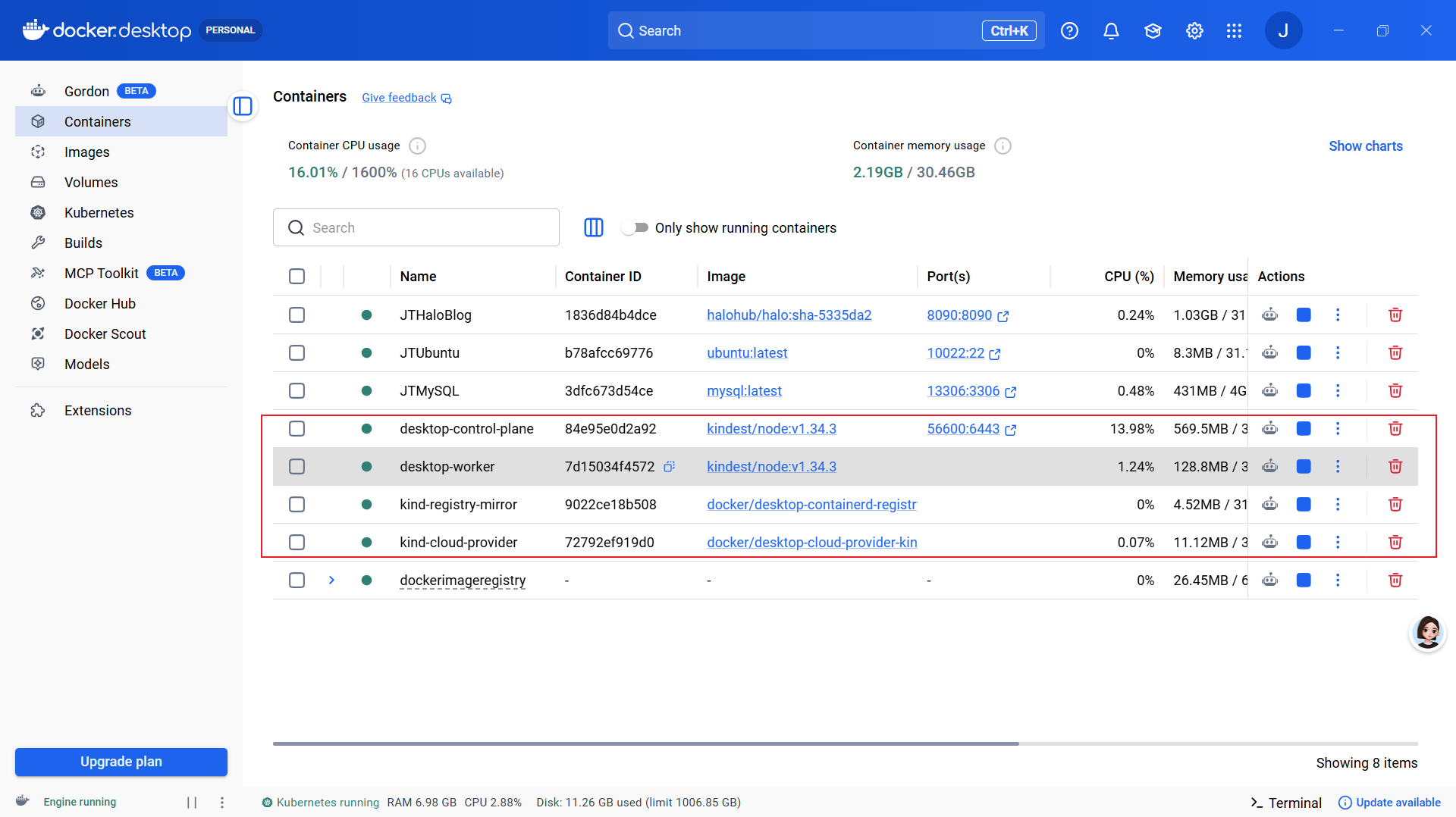
3、windows 下 docker desktop 中 K8s 集群
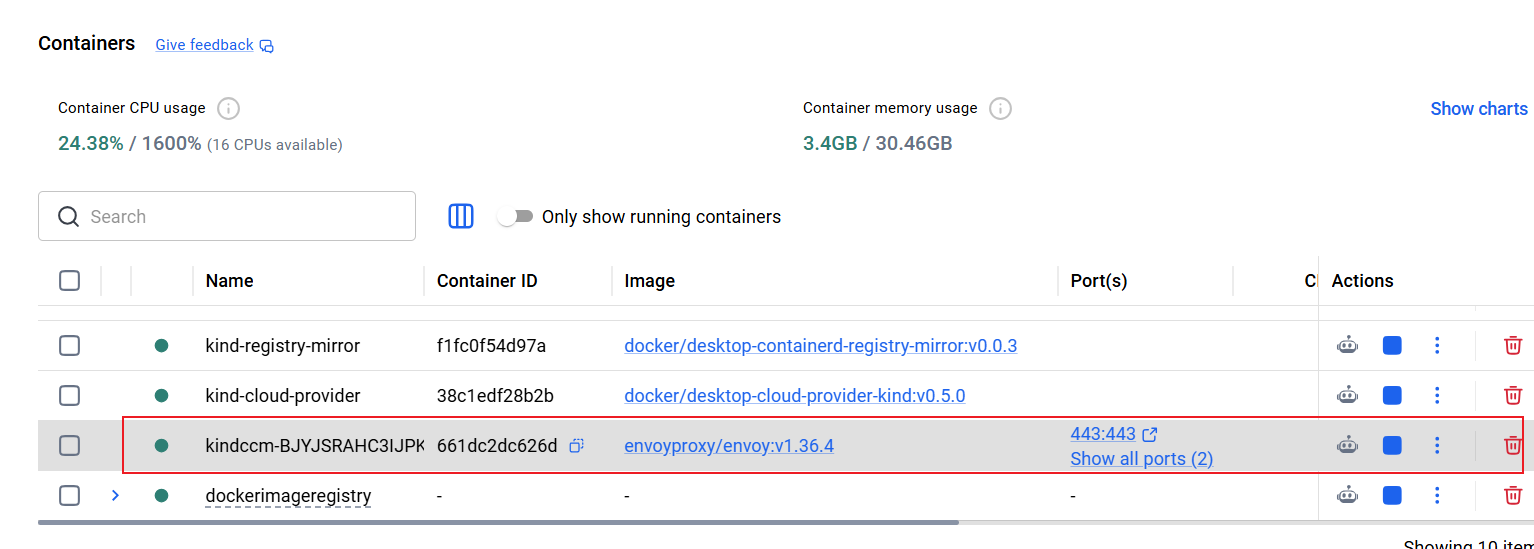
集群镜像包括:kindest/node、envoyproxy/envoy、docker/desktop-containerd-registry-mirror、docker/desktop-cloud-provider-kind
1. kindest/node:KIND 集群的 “节点模板镜像”
作用:模拟 K8s 节点的基础镜像,是 Kind 最核心的镜像。
内容:预装了特定版本 K8s 的全套组件(kubeadm、kubelet、kubectl、containerd、systemd),并提前拉好核心系统镜像(apiserver、etcd、coredns 等)。
场景:Docker Desktop 选 kind(多节点) 模式时,用它启动一个或多个容器,每个容器就是一个 K8s 节点(控制面 / 工作节点)。
示例:
kindest/node:v1.32.2代表 K8s 1.32.2 版本的节点镜像。
2. envoyproxy/envoy:高性能云原生代理(服务网格用)
作用:L4/L7 高性能代理服务器,云原生架构的核心网络组件。
内容:C++ 编写,支持 HTTP/2、gRPC、WebSocket,提供负载均衡、熔断、限流、动态配置(xDS)、全链路遥测等能力。
场景:
Docker Desktop K8s 中,服务网格(如 Istio)的数据平面核心,以 Sidecar 模式注入 Pod,拦截所有进出流量。
也可独立作 API 网关、边缘代理。
注意:Docker Desktop 启用 K8s 时默认不部署,仅当你安装 Istio 等服务网格时才会用到。
3. docker/desktop-containerd-registry-mirror:KIND 集群内的镜像缓存代理
作用:给 Kind 集群内的 containerd 做镜像加速 / 缓存,解决国内拉取 K8s 镜像慢、超时问题。
内容:轻量镜像仓库代理,缓存常用 K8s 系统镜像(如 kube-apiserver、etcd、coredns),集群内节点优先从本地缓存拉取,而非外网。
场景:Docker Desktop 内置,启用 Kind 集群时自动部署,提升集群启动速度和稳定性,减少外网依赖。
4. docker/desktop-cloud-provider-kind:Kind 集群的 “云厂商适配器”
作用:给本地 Kind 集群模拟云厂商能力,重点支持
LoadBalancer类型 Service。内容:实现 K8s 的
cloud-provider接口,把本地 Docker 网络和主机端口映射成 “云负载均衡器”,让本地集群也能用LoadBalancer暴露服务。场景:
Docker Desktop 启用 Kind 时默认部署,解决本地 Kind 集群无法用
LoadBalancer的痛点。支持 Gateway API,方便测试云原生网络功能。
容器包括:desktop-control-plane、desktop-worker、kind-registry-mirror、kind-cloud-provider
1. desktop-control-plane
K8s 集群的 “大脑 / 控制中心”
这是 K8s 主节点
里面跑着:
apiserver、etcd、scheduler、controller-manager作用:管理整个集群、接收指令、调度容器、存储状态
你执行的所有
kubectl命令,都是发给它
一句话:集群的总指挥。
2. desktop-worker
K8s 集群的 “工人 / 工作节点”
这是 K8s 工作节点
负责真正运行你的应用容器(Pod)
里面跑着:
kubelet、kube-proxy
一句话:真正干活、跑业务容器的节点。
3. kind-registry-mirror
本地镜像加速器 / 缓存仓库
Docker 官方给 Kind 集群做的本地镜像代理
作用:
加速拉取镜像
避免重复下载
解决国内网络拉取 K8s 镜像慢、失败问题
相当于集群内部的小 Docker Hub
一句话:让集群拉镜像更快、更稳。
4. kind-cloud-provider
云厂商模拟器(让本地集群拥有云能力)
作用:让你本地 Kind 集群支持 LoadBalancer 服务
没有它,你在 K8s 里创建:
yaml
type: LoadBalancer会一直
pending,无法外部访问。
一句话:让本地 K8s 能像云服务器一样暴露服务到外部。
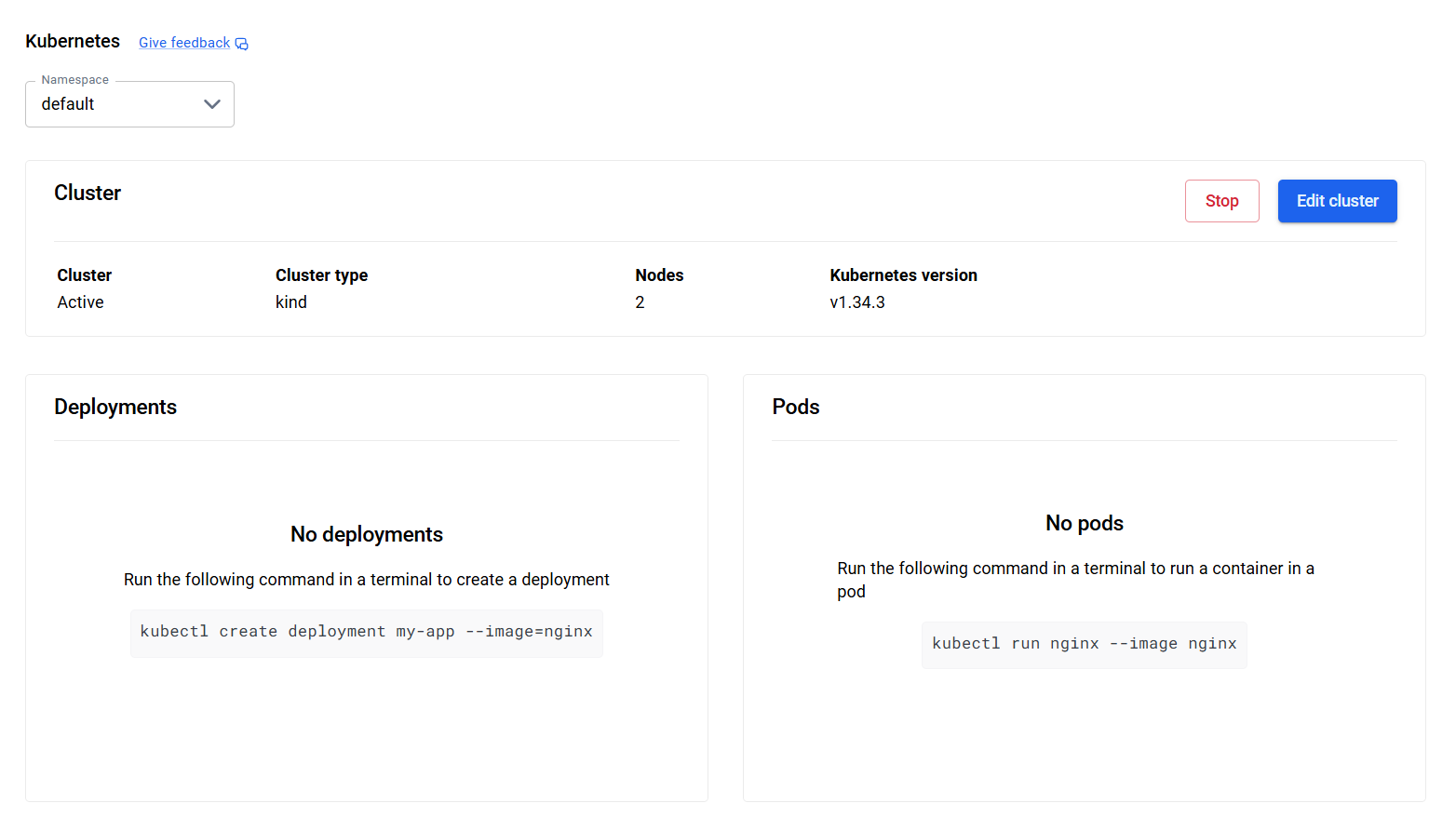
K8s控制面板
Namespace
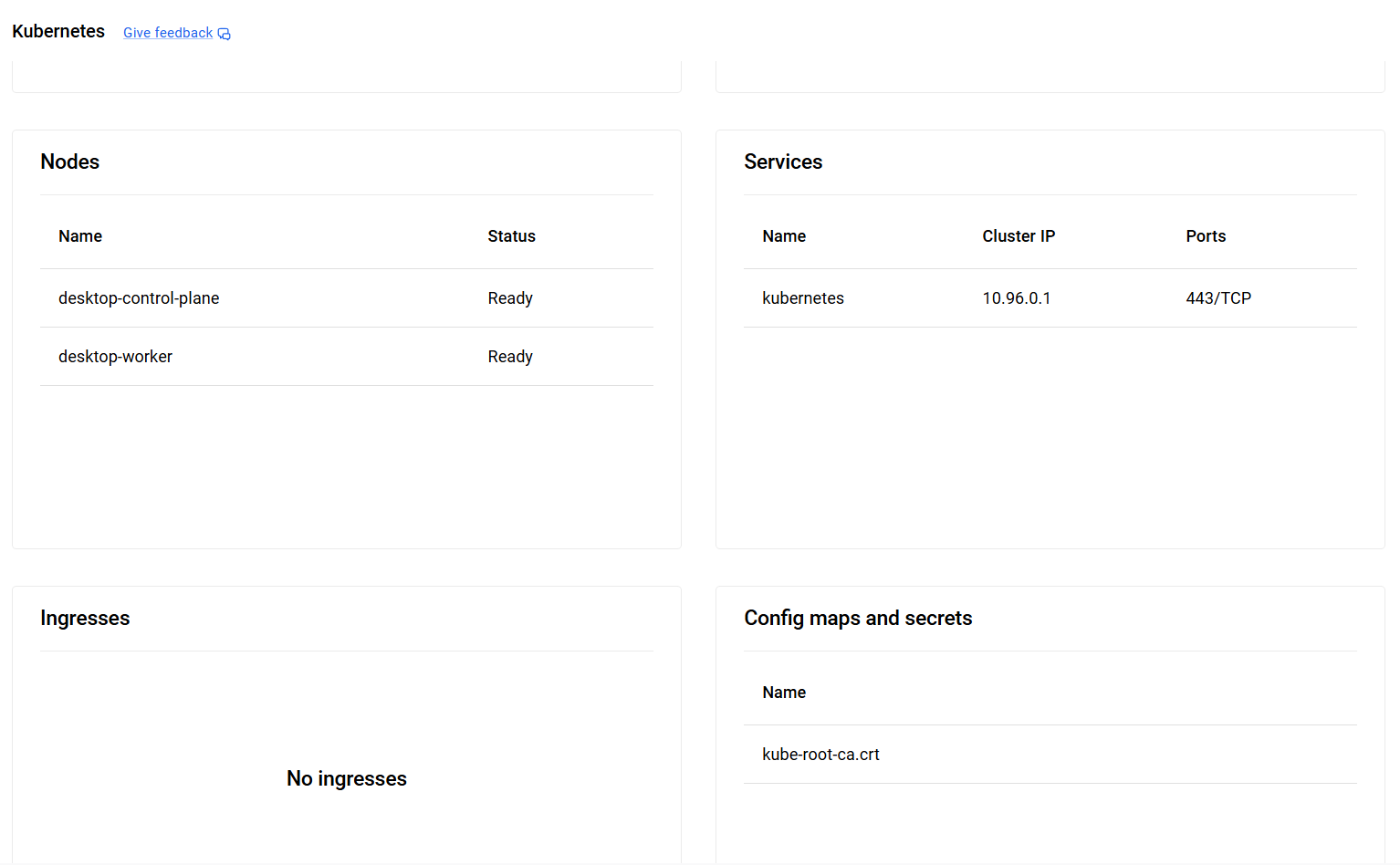
1. Nodes 节点
是什么:K8s 集群里的服务器(物理机 / 虚拟机)
干嘛的:
所有容器、Pod 都跑在 Node 上
集群的底层算力资源
类比:公司的办公电脑
2. Pods 容器组
是什么:K8s 最小调度单元,一个或多个容器打包在一起
干嘛的:
真正跑业务程序的地方
一个 Pod 共享网络、存储,一起启停
特点:不直接手动创建 Pod,一般由 Deployment 管理
类比:一个办公室,里面坐几个同事(容器)
3. Deployments 部署
是什么:管理 Pod 的控制器
干嘛的:
定义要跑多少个 Pod 副本
Pod 挂了自动重启、自动扩缩容
版本滚动更新 / 回滚(不停机发版)
场景:几乎所有常驻业务应用(Web、后端服务)都用它
类比:部门主管,负责招人、补人、换新人
4. Services 服务
是什么:Pod 的固定入口 / 负载均衡
干嘛的:
Pod 会漂移、IP 会变,Service 给一个稳定 IP / 域名
把请求转发给后端多个 Pod,做负载均衡
集群内部 / 外部访问入口
类型:ClusterIP (内部)、NodePort、LoadBalancer
类比:公司前台,外面找人不用找具体工位,找前台就行
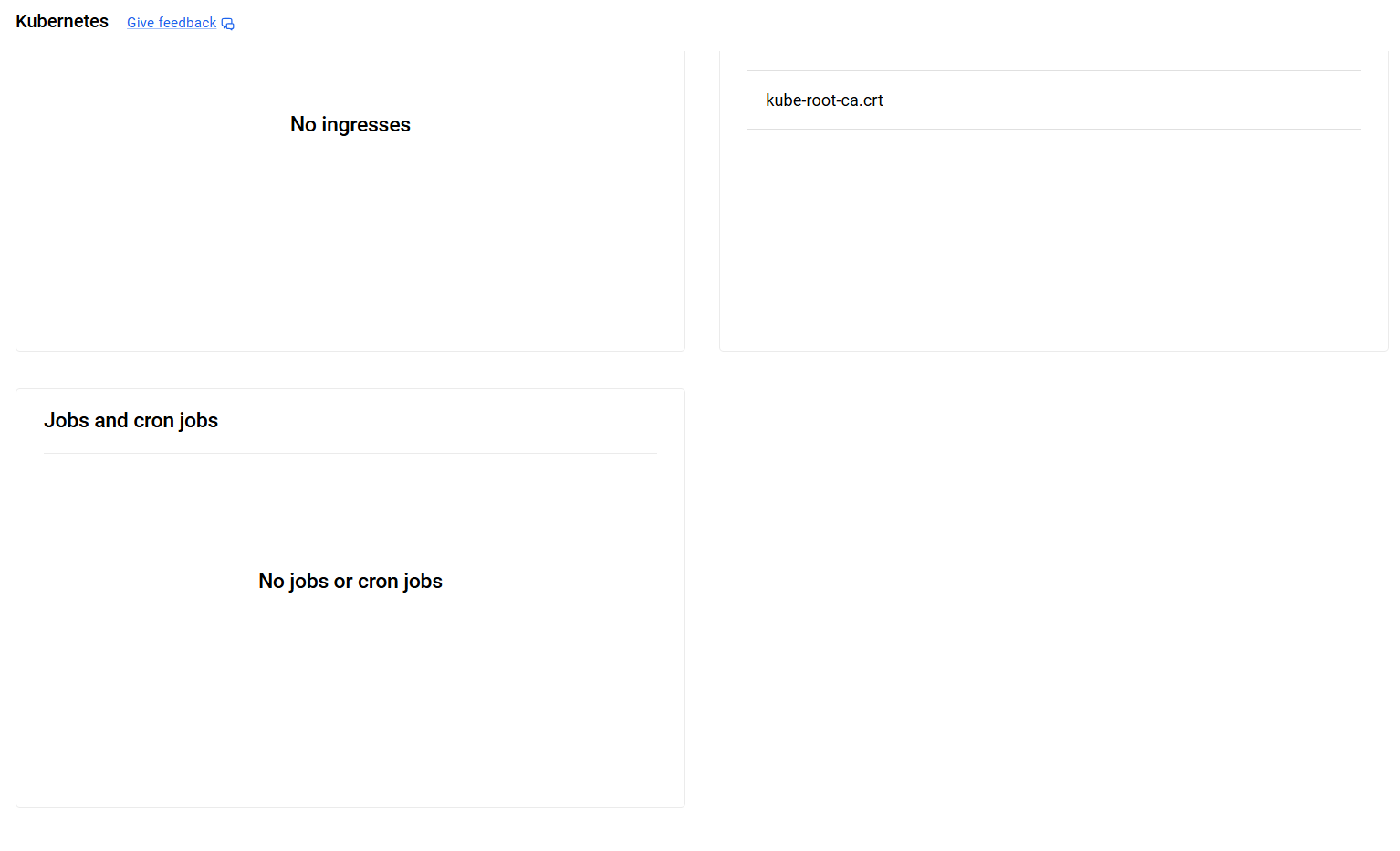
5. Ingresses 入口路由
是什么:七层 HTTP/HTTPS 网关路由
干嘛的:
用域名、路径转发到不同 Service
统一配置 SSL 证书、限流、路由规则
和 Service 区别:
Service 是四层 TCP/UDP;Ingress 是七层域名路由
类比:大楼总门禁 + 导视牌,按门牌分到不同部门
6. ConfigMaps & Secrets 配置和密钥
ConfigMap
存非敏感配置:配置文件、环境变量、参数
比如:数据库地址、超时时间、配置 JSON
Secret
存敏感数据:密码、Token、密钥、证书
会做基础加密,不能明文放配置里
干嘛的:把配置和代码解耦,不用改镜像就能改配置
7. Jobs & CronJobs 任务类
Job
一次性任务:跑一次就结束
比如:数据初始化、批量导入、一次性脚本执行
CronJob
定时任务:像 Linux crontab 定时执行
比如:凌晨定时备份、每天报表统计、定时清理日志
4、从 docker 私有仓库中拉取镜像部署到 k8s 中
前提条件:本地用 docker 部署了一个没有用户名密码的 docker-registry,在 docker-registry 中上传了一个简单的 myboot 镜像,myboot 镜像是springboot程序,端口号 9080。
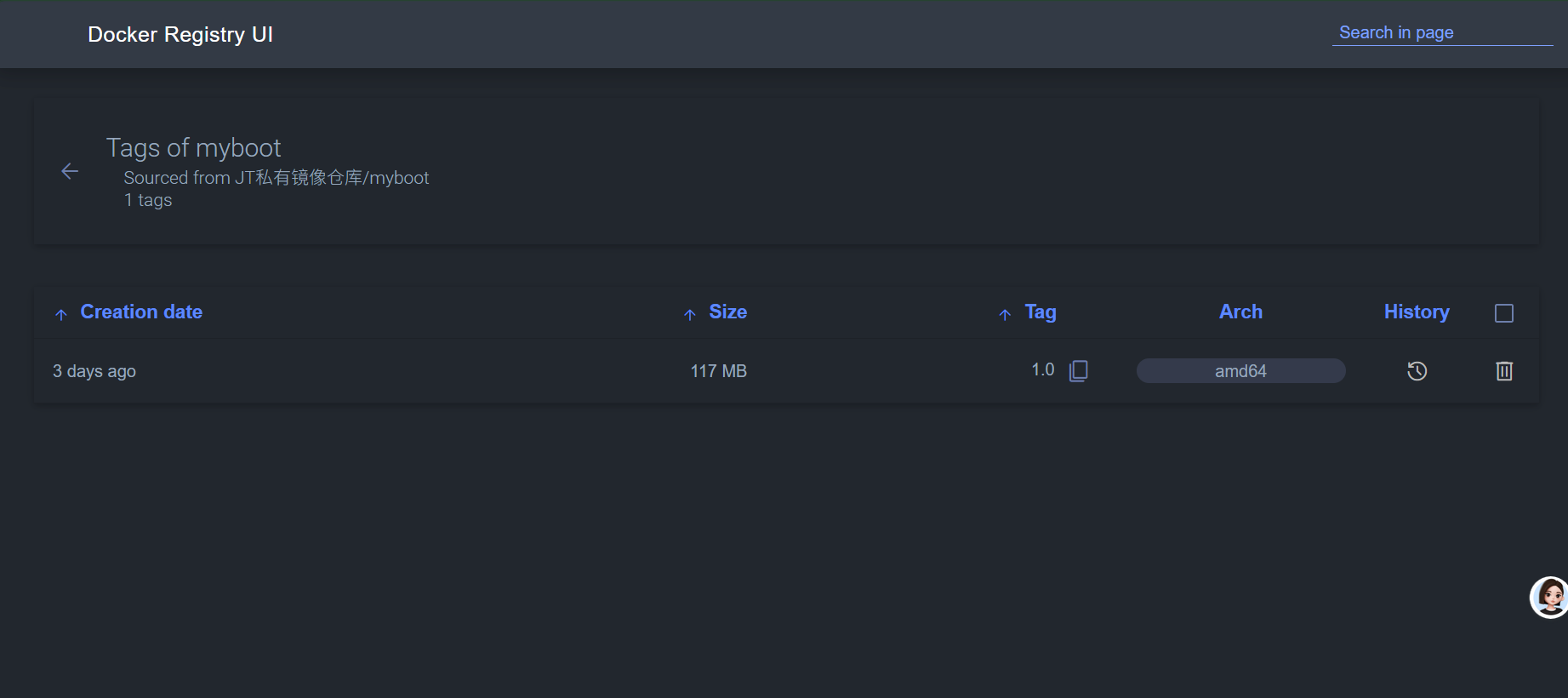
私有的 docker 镜像仓库的访问地址:localhost:15000
1、创建 secret 连接 docker 镜像仓库
# 这里 docker 的用户名密码,因为我的 docker 仓库没有,所以随便填的
kubectl create secret docker-registry jt-registry --docker-server=localhost:15000 --docker-username=1 --docker-password=12、通过 deployment 创建 pod,运行我的 springboot 程序
kubectl create deploy myboot --image=localhost:15000/myboot:1.03、通过 service 固定并暴露 pod 中 myboot 程序的访问端口
kubectl expose deployment myboot --port=9080 --type=NodePort4、查看 pod 和 service 信息
PS C:\Users\25472> kubectl get pod,svc -o wide
NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES
pod/myboot-565689886c-n4vdb 1/1 Running 0 38m 10.244.2.7 desktop-worker <none> <none>
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE SELECTOR
service/kubernetes ClusterIP 10.96.0.1 <none> 443/TCP 23h <none>
service/myboot NodePort 10.96.161.40 <none> 9080:30369/TCP 33m app=myboot5、k8s 部署 my-springboot 服务
5.1、前提条件
1、个人 docker 镜像仓库地址:localhost:15000
docker 镜像仓库 UI:localhost:15001
5.2、secret 连接私人镜像仓库
# 这里 docker 的用户名密码,因为我的 docker 仓库没有,所以随便填的
kubectl create secret docker-registry jt-registry --docker-server=localhost:15000 --docker-username=1 --docker-password=1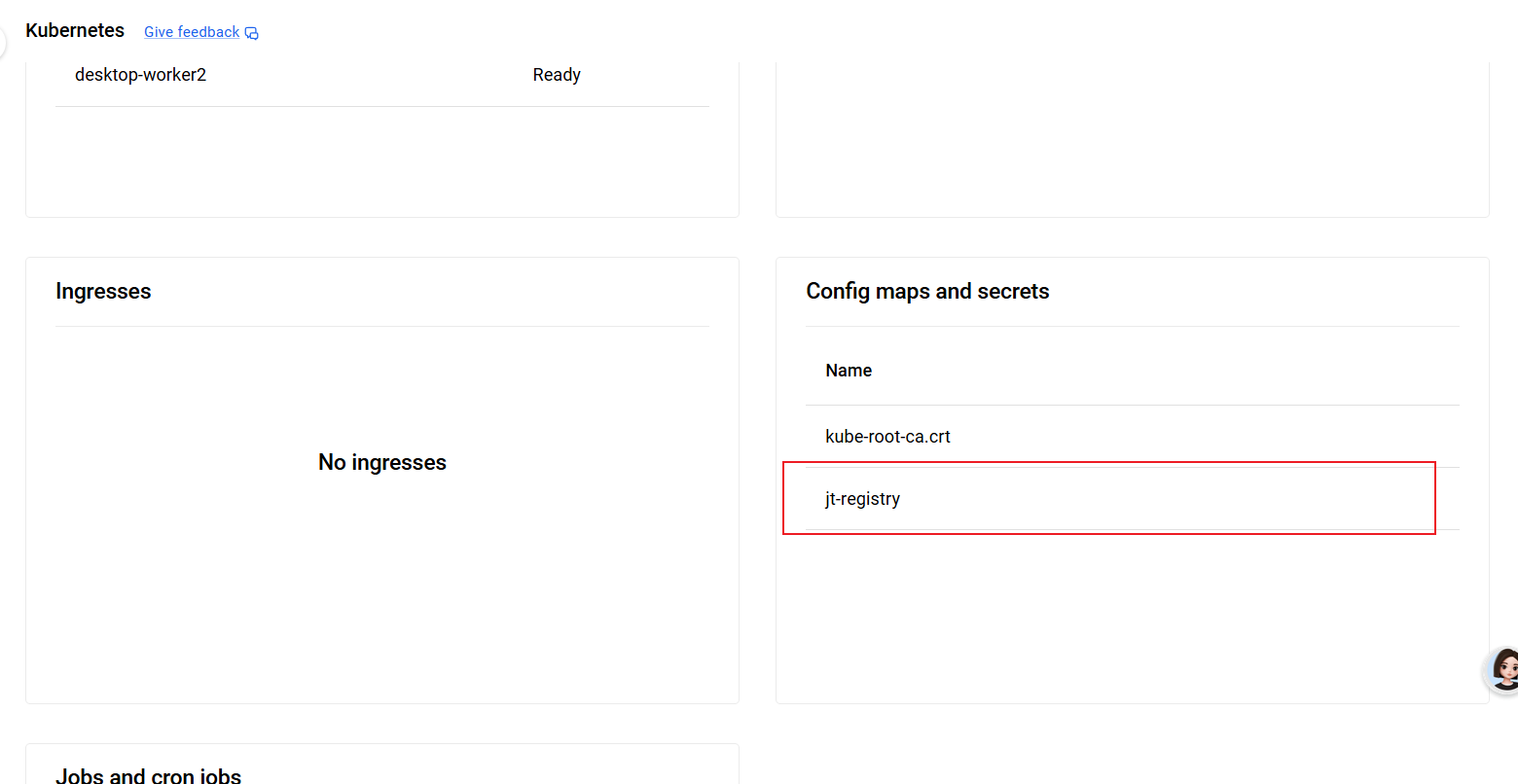
5.3、创建 deploy、pod、service
通过 myboot.yaml 文件创建 deployment、pod、service
kubectl apply -f D:\work\env\docker\K8s\myboot.yamlapiVersion: apps/v1
kind: Deployment
metadata:
name: myboot
spec:
replicas: 3 # 启动3个一模一样的Pod容器,k8s会自动将请求均匀分给3个Pod
selector:
matchLabels:
app: myboot
template:
metadata:
labels:
app: myboot
spec:
containers:
- name: myboot
image: localhost:15000/myboot:1.0 # 你的镜像名
ports:
- containerPort: 9080 # 你的项目端口
---
apiVersion: v1
kind: Service
metadata:
name: myboot
spec:
selector:
app: myboot
ports:
- port: 80 # Service 端口
targetPort: 9080 # 容器端口(你的 9080)5.4、通过 ingress 将服务端口暴露,提供给用户访问
1、安装 ingress-Nginx 控制器
通过vpn全局代理进行下载,否则下不下来
# 安装(自动创建 ingress-nginx 命名空间、RBAC、Deployment、Service)
kubectl apply -f https://raw.githubusercontent.com/kubernetes/ingress-nginx/controller-v1.8.2/deploy/static/provider/cloud/deploy.yaml
# 等待 Pod 就绪(1–2 分钟)
kubectl get pods -n ingress-nginx -w
# 验证(状态为 Running 即可)
kubectl get pods -n ingress-nginx
kubectl get svc -n ingress-nginxhttps://raw.githubusercontent.com/kubernetes/ingress-nginx/controller-v1.8.2/deploy/static/provider/cloud/deploy.yaml
apiVersion: v1
kind: Namespace
metadata:
labels:
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
name: ingress-nginx
---
apiVersion: v1
automountServiceAccountToken: true
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx
namespace: ingress-nginx
---
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
app.kubernetes.io/component: admission-webhook
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx-admission
namespace: ingress-nginx
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx
namespace: ingress-nginx
rules:
- apiGroups:
- ""
resources:
- namespaces
verbs:
- get
- apiGroups:
- ""
resources:
- configmaps
- pods
- secrets
- endpoints
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- coordination.k8s.io
resourceNames:
- ingress-nginx-leader
resources:
- leases
verbs:
- get
- update
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- create
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
labels:
app.kubernetes.io/component: admission-webhook
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx-admission
namespace: ingress-nginx
rules:
- apiGroups:
- ""
resources:
- secrets
verbs:
- get
- create
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx
rules:
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
- namespaces
verbs:
- list
- watch
- apiGroups:
- coordination.k8s.io
resources:
- leases
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- networking.k8s.io
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- networking.k8s.io
resources:
- ingresses/status
verbs:
- update
- apiGroups:
- networking.k8s.io
resources:
- ingressclasses
verbs:
- get
- list
- watch
- apiGroups:
- discovery.k8s.io
resources:
- endpointslices
verbs:
- list
- watch
- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/component: admission-webhook
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx-admission
rules:
- apiGroups:
- admissionregistration.k8s.io
resources:
- validatingwebhookconfigurations
verbs:
- get
- update
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx
namespace: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: ingress-nginx
subjects:
- kind: ServiceAccount
name: ingress-nginx
namespace: ingress-nginx
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
app.kubernetes.io/component: admission-webhook
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx-admission
namespace: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: ingress-nginx-admission
subjects:
- kind: ServiceAccount
name: ingress-nginx-admission
namespace: ingress-nginx
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: ingress-nginx
subjects:
- kind: ServiceAccount
name: ingress-nginx
namespace: ingress-nginx
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/component: admission-webhook
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx-admission
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: ingress-nginx-admission
subjects:
- kind: ServiceAccount
name: ingress-nginx-admission
namespace: ingress-nginx
---
apiVersion: v1
data:
allow-snippet-annotations: "true"
kind: ConfigMap
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx-controller
namespace: ingress-nginx
---
apiVersion: v1
kind: Service
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx-controller
namespace: ingress-nginx
spec:
externalTrafficPolicy: Local
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- appProtocol: http
name: http
port: 80
protocol: TCP
targetPort: http
- appProtocol: https
name: https
port: 443
protocol: TCP
targetPort: https
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
type: LoadBalancer
---
apiVersion: v1
kind: Service
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx-controller-admission
namespace: ingress-nginx
spec:
ports:
- appProtocol: https
name: https-webhook
port: 443
targetPort: webhook
selector:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
type: ClusterIP
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx-controller
namespace: ingress-nginx
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
spec:
containers:
- args:
- /nginx-ingress-controller
- --publish-service=$(POD_NAMESPACE)/ingress-nginx-controller
- --election-id=ingress-nginx-leader
- --controller-class=k8s.io/ingress-nginx
- --ingress-class=nginx
- --configmap=$(POD_NAMESPACE)/ingress-nginx-controller
- --validating-webhook=:8443
- --validating-webhook-certificate=/usr/local/certificates/cert
- --validating-webhook-key=/usr/local/certificates/key
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: LD_PRELOAD
value: /usr/local/lib/libmimalloc.so
image: registry.k8s.io/ingress-nginx/controller:v1.8.1@sha256:e5c4824e7375fcf2a393e1c03c293b69759af37a9ca6abdb91b13d78a93da8bd
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
livenessProbe:
failureThreshold: 5
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
name: controller
ports:
- containerPort: 80
name: http
protocol: TCP
- containerPort: 443
name: https
protocol: TCP
- containerPort: 8443
name: webhook
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
resources:
requests:
cpu: 100m
memory: 90Mi
securityContext:
allowPrivilegeEscalation: true
capabilities:
add:
- NET_BIND_SERVICE
drop:
- ALL
runAsUser: 101
volumeMounts:
- mountPath: /usr/local/certificates/
name: webhook-cert
readOnly: true
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
serviceAccountName: ingress-nginx
terminationGracePeriodSeconds: 300
volumes:
- name: webhook-cert
secret:
secretName: ingress-nginx-admission
---
apiVersion: batch/v1
kind: Job
metadata:
labels:
app.kubernetes.io/component: admission-webhook
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx-admission-create
namespace: ingress-nginx
spec:
template:
metadata:
labels:
app.kubernetes.io/component: admission-webhook
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx-admission-create
spec:
containers:
- args:
- create
- --host=ingress-nginx-controller-admission,ingress-nginx-controller-admission.$(POD_NAMESPACE).svc
- --namespace=$(POD_NAMESPACE)
- --secret-name=ingress-nginx-admission
env:
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
image: registry.k8s.io/ingress-nginx/kube-webhook-certgen:v20230407@sha256:543c40fd093964bc9ab509d3e791f9989963021f1e9e4c9c7b6700b02bfb227b
imagePullPolicy: IfNotPresent
name: create
securityContext:
allowPrivilegeEscalation: false
nodeSelector:
kubernetes.io/os: linux
restartPolicy: OnFailure
securityContext:
fsGroup: 2000
runAsNonRoot: true
runAsUser: 2000
serviceAccountName: ingress-nginx-admission
---
apiVersion: batch/v1
kind: Job
metadata:
labels:
app.kubernetes.io/component: admission-webhook
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx-admission-patch
namespace: ingress-nginx
spec:
template:
metadata:
labels:
app.kubernetes.io/component: admission-webhook
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx-admission-patch
spec:
containers:
- args:
- patch
- --webhook-name=ingress-nginx-admission
- --namespace=$(POD_NAMESPACE)
- --patch-mutating=false
- --secret-name=ingress-nginx-admission
- --patch-failure-policy=Fail
env:
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
image: registry.k8s.io/ingress-nginx/kube-webhook-certgen:v20230407@sha256:543c40fd093964bc9ab509d3e791f9989963021f1e9e4c9c7b6700b02bfb227b
imagePullPolicy: IfNotPresent
name: patch
securityContext:
allowPrivilegeEscalation: false
nodeSelector:
kubernetes.io/os: linux
restartPolicy: OnFailure
securityContext:
fsGroup: 2000
runAsNonRoot: true
runAsUser: 2000
serviceAccountName: ingress-nginx-admission
---
apiVersion: networking.k8s.io/v1
kind: IngressClass
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: nginx
spec:
controller: k8s.io/ingress-nginx
---
apiVersion: admissionregistration.k8s.io/v1
kind: ValidatingWebhookConfiguration
metadata:
labels:
app.kubernetes.io/component: admission-webhook
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.8.1
name: ingress-nginx-admission
webhooks:
- admissionReviewVersions:
- v1
clientConfig:
service:
name: ingress-nginx-controller-admission
namespace: ingress-nginx
path: /networking/v1/ingresses
failurePolicy: Fail
matchPolicy: Equivalent
name: validate.nginx.ingress.kubernetes.io
rules:
- apiGroups:
- networking.k8s.io
apiVersions:
- v1
operations:
- CREATE
- UPDATE
resources:
- ingresses
sideEffects: None验证执行结果
PS C:\Users\25472> kubectl apply -f https://raw.githubusercontent.com/kubernetes/ingress-nginx/controller-v1.8.2/deploy/static/provider/cloud/deploy.yaml
namespace/ingress-nginx unchanged
serviceaccount/ingress-nginx unchanged
serviceaccount/ingress-nginx-admission unchanged
role.rbac.authorization.k8s.io/ingress-nginx unchanged
role.rbac.authorization.k8s.io/ingress-nginx-admission unchanged
clusterrole.rbac.authorization.k8s.io/ingress-nginx unchanged
clusterrole.rbac.authorization.k8s.io/ingress-nginx-admission unchanged
rolebinding.rbac.authorization.k8s.io/ingress-nginx unchanged
rolebinding.rbac.authorization.k8s.io/ingress-nginx-admission unchanged
clusterrolebinding.rbac.authorization.k8s.io/ingress-nginx unchanged
clusterrolebinding.rbac.authorization.k8s.io/ingress-nginx-admission unchanged
configmap/ingress-nginx-controller unchanged
service/ingress-nginx-controller unchanged
service/ingress-nginx-controller-admission unchanged
deployment.apps/ingress-nginx-controller configured
job.batch/ingress-nginx-admission-create unchanged
job.batch/ingress-nginx-admission-patch unchanged
ingressclass.networking.k8s.io/nginx unchanged
validatingwebhookconfiguration.admissionregistration.k8s.io/ingress-nginx-admission configured
PS C:\Users\25472> kubectl get pods -n ingress-nginx -w
NAME READY STATUS RESTARTS AGE
ingress-nginx-admission-create-m8cr7 0/1 Completed 0 78m
ingress-nginx-admission-patch-n49m8 0/1 Completed 2 78m
ingress-nginx-controller-7cfc9845c9-zhx8s 1/1 Running 0 78m
PS C:\Users\25472> kubectl get pods -n ingress-nginx
NAME READY STATUS RESTARTS AGE
ingress-nginx-admission-create-m8cr7 0/1 Completed 0 78m
ingress-nginx-admission-patch-n49m8 0/1 Completed 2 78m
ingress-nginx-controller-7cfc9845c9-zhx8s 1/1 Running 0 78m
PS C:\Users\25472> kubectl get svc -n ingress-nginx
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
ingress-nginx-controller LoadBalancer 10.96.126.244 172.18.0.7 80:32544/TCP,443:32177/TCP 78m
ingress-nginx-controller-admission ClusterIP 10.96.90.105 <none> 443/TCP 78m2、配置 ingress 规则并执行
通过配置 ingress.yaml ,根据内部的 ingress-nginx 转发 myboot 服务端口
kubectl apply -f D:\work\env\docker\K8s\ingress.yamlapiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: jt-ingress
spec:
ingressClassName: nginx # 关键,绑定 ingress-nginx 控制器
rules:
- host: localhost # 本地域名,随便写
http:
paths:
- path: /
pathType: Prefix
backend:
service:
name: myboot
port:
number: 80验证 ingress 安装结果
PS C:\Users\25472> kubectl get ingress
NAME CLASS HOSTS ADDRESS PORTS AGE
jt-ingress nginx localhost 172.18.0.7 80 3m22s5.5、注意
1、localhost访问失败
依照上述流程创建后,出现无法访问 localhost 的情况,应该是手动删除了 envoyproxy/envoy:v1.36.4 镜像生成的容器, 但没有彻底清除之前安装的 ingress-nginx ,所以需要删除之前安装的 ingress-nginx ,并确定删除干净。
# 删除 ingress-nginx 所有资源
kubectl delete -f https://raw.githubusercontent.com/kubernetes/ingress-nginx/controller-v1.8.2/deploy/static/provider/cloud/deploy.yaml
# 确认删除干净
kubectl get pods -n ingress-nginx2、重启 deploy、pod、svc
kubectl delete -f D:\work\env\docker\K8s\myboot.yaml
kubectl apply -f D:\work\env\docker\K8s\myboot.yaml


评论交流
欢迎留下你的想法